In this hyper-connected world, it is vital to stay ahead of cybercriminals by testing your existing enterprise security through real-world simulations and filling in the loopholes. We, at Agnos, can advise you on your healthcare security strategy, implement solutions customized to the Healthcare industry, and manage your security operations holistically. We help you use security to both defend the enterprise against malicious threats and enable the enterprise to operate new business processes while maintaining acceptable levels of risk. Whether it's a data breach, insecure APIs, cloud abuse, malware attack, hacking, insecure single-factor passwords, shadow IT systems, or architectural loopholes in IoT implementation, we help you detect, prevent, and respond to these attacks in the best possible way.
Here’s how we can help:
- Requirement Analysis: Identify a holistic set of security & regulatory compliance requirements specific to your business to offer futuristic solutions that can maximize ROI, mitigate risk, and enhance efficiency.
- Data-driven Strategy: Use analytics to recognize patterns and loopholes, and isolate the root causes of current problems to develop a comprehensive enterprise security strategy that can effectively tackle security challenges that come with the digitization of business processes.
- Implementation: Integrating elements of compliance, threat and vulnerability management, security strategy, and governance in the security architecture across the enterprise technology systems. We help you with identity and access management, app and infrastructure security, data protection and privacy services, and more.
- Collaboration: Leveraging our global associations and advanced technological know-how, we also help align the right technology partners with your security needs, where required, to enhance security capabilities and increase cost-efficiency.

Application and Infrastructure Security
We can help you develop a comprehensive application security program and establish an enterprise-grade application security program to drive security-focused software development for your healthcare applications. We can provide secure software development training that installs a strong application security expertise baseline in the software development lifecycle. We offer container security services that include assessment, solution design, implementation, and managed services for container security. We can help you with application security threat modeling that enables a threat-driven secure software development approach to strengthen the security architecture and posture. We can offer application penetration testing that identifies code-level vulnerabilities, run-time security defects, and application logic flaws. We can help you connect security with DevOps which are often disjointed and including people, processes, and tooling.
We can help you maintain application security with our complimentary cloud and infrastructure security services. We can help you understand the future state of your business and risk-based security program, establishing cloud security at every layer of the stack to enable your business goals. We can help you integrate native cloud security controls, implement a secure-by-design methodology, and establish security orchestration and automation to define and enforce your enterprise cloud security program. In short, we can help you execute continuous threat management and resiliency to monitor and adapt to the threat landscape — detect and contain attacks and orchestrate an effective organization-wide incident response. We offer hybrid multi-cloud security solutions beginning with a holistic cloud security risk-based strategy, governance, and readiness plan. We help you establish workload protection and deploy secure workloads that are secure-by-design. We help you manage threat and event information with precise insights to adapt to new threats and rapidly detect and respond to attacks.
We help you assess who has access to your most critical workloads and systems, and identify and manage who has appropriate levels of access across your hybrid multi-cloud environment. We help you explore cloud access management and authentication solutions and explore cloud identity and access management services to create a hybrid multi-cloud security platform where you can integrate your existing security tools to gain insight across your environment.We help you connect to existing data sources without moving your data, and act faster with orchestration and automation across your tools and teams.
Identity and Access Management
We implement the next-gen processes and tools to centralize and streamline access within the enterprise across physical and virtual assets and facilities. We help Healthcare enterprises with the application of the latest technologies such as AI and machine learning to strengthen identity and access management systems and help them establish an on-going comprehensive risk management program. We make sure that employees, partners, customers, and suppliers get the right access at the right time, in a secure way, to ensure productivity while managing risks. We also offer to outsource and manage services to help our Healthcare clients focus on their core competencies and reduce costs while minimizing risk.
Data Protection and Privacy
We help you identify business processes that pose a risk of accidental disclosures or data breaches, and help fill in the gaps efficiently and swiftly. We re-engineer and implement Healthcare processes so that people and technology work together to prevent incidents that affect and jeopardize your business and reputation.We identify and classify confidential data, and document the data ownership to safeguard data loss in addition to helping your organization understand the right data handling processes. We conduct sensitive data flow analysis and protect stored data against unauthorized access by helping you build the right data architecture and platform capabilities.
Why Agnos?
As IT organizations continue to struggle to find the time and resources to adequately focus on ever-growing enterprise security risks, it is significant to find a trusted advisor who can help develop a comprehensive enterprise security strategy that considers the realities of client constraints such as budget limitations, skills gaps, and the rapidly changing security threat landscape.
At Agnos, we put business value and an independent perspective in front of every security engagement we deliver. Our goal is to make sure nothing disrupts your desired business outcomes and you are well-prepared to respond to any threats your organization may face in a timely and effective way.
Here are a few more compelling reasons to choose us over any other service providers:
- We help your organization move to proactive defense and value-creation when confronting security challenges and consider our relationship with you in managing your enterprise security as strategic and not transactional. Our top priority is your bottom line.
- We help you effectively manage the growing complexity in IAM, given the Bring Your Own Device (BYOD) paradigm shift and the dynamic forces of change driving greater merger, acquisition, and divestiture activity.
- We bring deep industry expertise and leverage world-class experts, such as former Chief Information Security Officers (CISO) with extensive experience in the trenches (e.g. National Security Agency) and a profound understanding of cyber threats and the measures to protect against them.
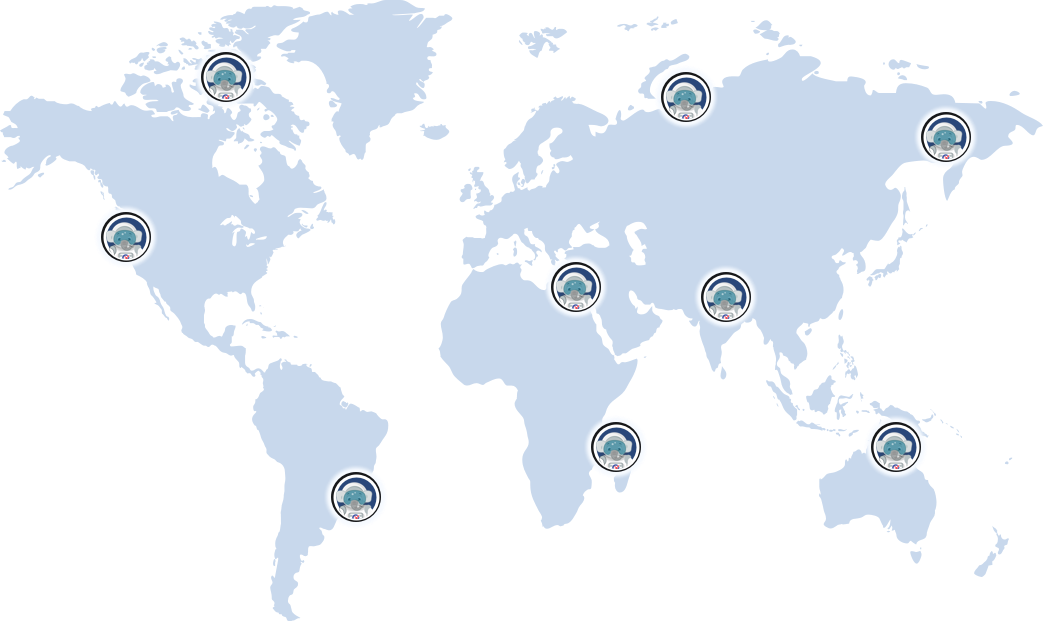
- We along with our smart strategic alliance partners bring an array of proven tools and techniques to address your enterprise security challenges and offer a global delivery network of skilled practitioners available round the clock to enhance business agility while reducing your costs.
- We offer need-driven partner solutions through our strategic alliances, unlike many other companies that are driven by referral fees and incentives. Also, all the compensation we receive from any partner is passed back to the client as service credits.
- Our Gain Share Model ensures that we deliver the business outcomes you seek. We want our clients to pay for actual performance and measurable results rather than slick presentations.
- We build the cost to serve models and business cases to help you demonstrate to the senior business and IT leadership the quantitative and qualitative impact of investing in enterprise security, which is becoming highly unmanageable and costly for the businesses.
- We help you embed a culture of security and risk management across your IT organization to make you adequately prepared for fast-moving potential security events and ready to respond in a quick and organized way.
Get in Touch With Us
Let's help you
navigate your Goals
Based in Miami, FL, Agnos offers superior healthcare enterprise security services to help you effectively manage risks and build cyber resilience across the enterprise. With our elaborative industry experience and skilled software engineers, we can help you craft customized healthcare-specific security solutions.





